

Removed by mod
I’m just this guy, you know?


Removed by mod


#### MAXLOGAGE=24.0
Up to how many hours of queries should be imported from the database and logs? Values greater than the hard-coded maximum of 24h need a locally compiled `FTL` with a changed compile-time value.
I assume this is the setting you are suggesting can extend the query count period. It still will only give you the last N hours’ worth of queries, which is not what OP asked. I gather OP wants to see the cumulative total of blocked queries over all time, and I doubt the FTL database tracks the data in a usable way to arrive at that number.


Ah, well if you know differently then please do share with the rest of us? I think the phrasing in my post makes it pretty clear I was open to being corrected.


So, like a running sum? No, I don’t think so, not in Pi-hole at least.
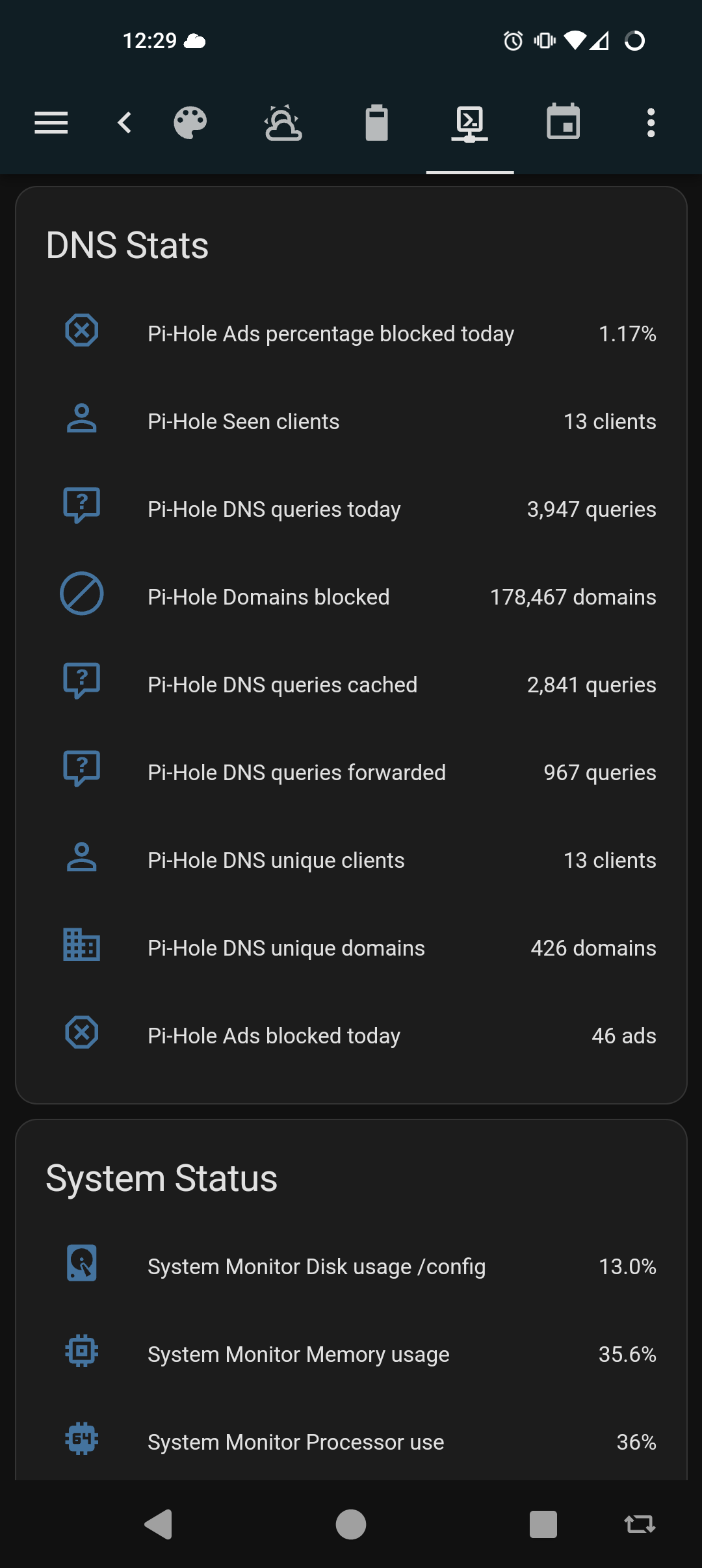
Pi-hole does have an API you could scrape, though. A Prometheus stack could track it and present a dashboard that shows the summation you want. There are other stats you could pull as well. This is a quick sample of what my home assistant integration sees


That counter, I believe, for the last 24 hours. It will fluctuate up and down across your active daily periods


Unless I misunderstand your question, draw.io can be downloaded as a standalone Linux application and run locally.
Likewise, the Xfig package should he available in most Linux repos. It’s old, but good enough for a quick sketch.
edit: aha. My mistake. My eyes slid over ‘open source’ in the title*, and even still I hadn’t realized it was an Apache license.
* Whaaat, it was pre-coffee? Let the purest among us cast the first stone.


This just in, scientists unveil “a loop of wire”
I keed, I keed. Glad to see materials science improving technologies we have for new applications.
Unbound will take updates via API. You could either write exit hooks on your clients, or use the “on commit” event on isc-dhcp-server to construct parameters and execute a script when a new lease is handed out.
I used to selfhost more, but honestly it started to feel like a job, and it was getting exhausting (maybe also irritating) to keep up with patches & updates across all of my services. I made decisions about risks to compromise and data loss from breaches and system failures. In the end, In decided my time was more valuable so now I pay someone to incur those risks for me.
For my outward facing stuff, I used to selfhost my own DNS domains, email + IMAP, web services, and an XMPP service for friends and family. Most of that I’ve moved off to paid private hosting. Now I maintain my DNS through Porkbun, email through MXroute, and we use Signal instead of XMPP. I still host and manage my own websites but am considering moving to a ghost.org account, or perhaps just host my blogs on a droplet at DO. My needs are modest and it’s all just personal stuff. I learned what I wanted, and I’m content to be someone else’s customer now.
At home, I still maintain my custom router/firewall services, Unifi wireless controller, Pihole + unbound recursive resolver, Wireguard, Jellyfin, homeassistant, Frigate NVR, and a couple of ADS-B feeders. Since it’s all on my home LAN and for my and my wife’s personal use, I can afford to let things be down a day or two til I get around to fixing it.
Still need to do better on my backup strategies, but it’s getting there.


I use Porkbuns API. It’s not sophisticated, but it works.


Gandi changed their TOS and price structure last year, so I ported everything over to Porkbun for a small savings, but mostly as a big middle finger to Gandi.
If you’re gonna get banged that kind of cash for functions you’re already using, you may as well look at better registrars, and get better value for your spend.
Shop around.
You could source a pair of gigabit media converters and a length of fiber on Amazon for about $100. Just use the media converters to extend the Ethernet port from where the Internet hands off in your house over to your office. You can affix the fiber along baseboards and up over door frames with adhesive cleats and zip ties, or those nylon staples on a nail they use to tack down coax cable.
If you’re willing to spend a little more on the fiber for a custom color, you can probably even order the fiber in a more neutral color than SMF yellow to blend into the trim better.
If you just want each physical interface on your server to participate in a single VLAN, set the corresponding switch port as an access port in the desired VLAN, and then configure each server interface as a normal untagged interface.
You would only do tagged frames (802.1q trunking) if you wanted to support several VLANs on the switch port.


deleted by creator


It’s mainly about managing risk, but also not all ISPs allow residential accounts to host services on their IP addresses.
Opening a port to the internet exposes the service to the whole internet, which means you need to secure the service with strong credentials, set up SSL, manage the certificate, and keep software up to date. You incur a lot of extra work, and also extra risk not only to your self-hosted service, but to any other services you host that “trust” your service.
All that work requires extra knowledge and experience to get right which, let’s just be honest here: we’ve all probably followed that one How-To blog post, and maybe not understood every step along the way to get past that one pesky error.
Running a secure VPN overlay like Tailscale has much less overhead. You generate some keys, and configure your lighthouse server so the enrolled devices can find each other. It effectively extends your LAN environment to trusted hosts wherever they might be without exposing any of the services to the Internet.
Overall, Tailscale is simpler and much less work for individuals to set up and maintain than to secure multiple services against casual or targeted intrusion.
Tailscale also has the benefit of being a “client” in the view of the ISP, who see your IP address reach out to your VPS to initiate the tunnel, and not the other way around. If there’s any CGNAT going on, Tailscale would tunnel through it.


Its not exactly lightweight, but the Netdata integration will get you all of that.
Securing Netdata itself can be a bit of a chore, and then the integration requires creating sensors of interest in your configuration.yaml file. Have a look, it might be an interesting project if you’re up for a challenge.
Curious to hear what others are thinking too.
I appreciate the pun!
For home networks, I agree there’s usually not a need. I do it for portability reasons: I always use 192.168.0.0/24 addresses (192.168.0.0 - 192.168.0.255) for services I’m hosting on prem at home. In general, my home router is a Linux box connected directly to my ISP’s network on one interface and a switch with several VLANs on its other interface, and which has IP forwarding enabled with IP masquerade. I also use IPv6 a fair amount and receive a healthy whack of addresses from my ISP that I delegate out portions of to each VLAN. By my count I have 6 or 8 active VLANs on my home net for the adults, for work, for the kids, for the central services, for isolating untrustworthy IOT doodads, for infrastructure management, and for guests.
Most of my so-called central services have been hosted on the same Linux box that does the routing, using containers bount do tjose subnet zero IPs on the loopback. It skeeves me out a bit to do that though, so I’ve been moving that stuff over to a new applications server in a DMZ VLAN. I know what I’m doing, but I’m also incurring unnecessary risks having structured my service hosting the way I have.
The IP-on-loopback trick let’s.me move those services from a VIP on the router to an IP on the new service host without having to reconfigure everything. I just fake in some /32 routes where I need to, and the traffic goes where I want of to.
I admit up front this isn’t great discipline, but as I said I know what I’m doing and it only sounds crazy to me when I try to explain it to other people. Lol.
I do this, but I also work in tech and have a pretty solid grasp of routing and how that all works. I agree it may seem overkill for many installs, but makes sense for certain use cases. I’ll try to explain without writing a book. I’ll be glossing over a LOT of texture in the following…
In networking, a router is considered to be a node in a graph with multiple host IP addresses, one for each edge. It has an interface-- sometimes physical but more often viirtual-- on each edge (network segment, VLAN) that connects to it, and which usually serves as the gateway IP for that edge. In larger networks where there is more than a single router, the routers must all tell each other which router has which destination network segment, so they all speak a routing protocol like RIP, OSPF or IS-IS. Each of the speakers must be able to identify itself uniquely among the others so the others know which node is making what advertisements. To do this, they each are assigned a unique router ID, which is normally a 32 bit integer value represented as a dotted quad. Customarily this is an IP address, and the protocols further this idea by adopting the highest numbered IP address on the device or the addrss of its loopback interface, if defined.
The point of a routing protocol is for the participating nodes to advertise IP ranges associated with their connected edges. They assert advertisements for each edge when it is active.(I.e., the interface is UP) and withdraw or expire them when the edge is unavailable (I.e., the interface is in any state other than UP). Every time an edge changes state-- goes from UP to not-UP, or not-UP to UP-- that advertisement must propagate across the whole system, and every node must stop forwarding traffic to recalculate its own best path to the remaining available edges. This is called reconvergence, and network engineers try to do things to minimize the number and frequency of these events.
Practically, one of the things network engineers do to try to avoid instability is not having the ID of a speaker change dynamically. Going back to how the device selects its router ID, it considers the loopback IP first, or else the highest numbered IP active on the device at the time of evaluation. Edge interfaces can go UP or not-UP for any number of reasons at any time, thus they are less than ideal to use for the router ID. The loopback interface by contrast is always up. This interface is typically assigned the IP the routing protocol will use for its router ID.
In practice, the loopback is the only interface on a router than can be said to belong to the router itself¹, and not to an edge connected to the router². There are other practical reasons in routing to do this, but they all come back to the fact that the loopback is always up, and therefore it’s always apt to be advertised as an available edge.
So what does any of this have to do with servers, applications and self hosting?
Applications that provide services over the network, DNS servers for example, need to bind to at least one IP address and protocol port. On servers with multiple interfaces, these applications normally bind to all available interface addresses, using the address 0.0.0.0. In some situations this might be undesirable. Maybe you don’t want your pihole serving your internal DNS to your ISP, or maybe you have several VLANs at your house and want to use a single IP address for DNS across all of your VLANs, or you don’t trust the VLAN interface IPs to always be the same.
Adding an IP to the lo interface ensures that IP is always available and reachable. It provides a single place for all hosts in the system to go that isn’t pinned to any one of the possible VLAN interface IPs.
In my own home setup, I define several IPs on the loopback for different containers that all want to use port 8443/tcp for their public port. This gives me the flexibility of being able to assign different services their own IP (which I can then reference by name in DNS) on their native port vis-à-vis the documentation. So my Pihole container has its address and my Unifi controller container has its own as well.
Anyway, this is very much a Done Thing in the industry. Not everyone needs it, but its a useful technique in the right circumstances.
No worries, the other poster was just wasn’t being helpful. And/or doesn’t understand statistics & databases, but I don’t care to speculate on that or to waste more of my time on them.
The setting above maxes out at 24h in stock builds, but can be extended beyond that if you are willing to recompile the FTL database with different parameters to allow for a deeper look back window for your query log. Even at that point, a second database setting farther down that page sets the max age of all query logs to 1y, so at best you’d get a running tally of up to a year. This would probably at the expense of performance for dashboard page loads since the number is probably computed at page load. The live DB call is intended for relatively short windows vs database lifetime.
If you want an all-time count, you’ll have to track it off box because FTL doesn’t provide an all-time metric, or deep enough data persistence. I was just offering up a methodology that could be an interesting and beneficial project for others with similar needs.
Hey, this was fun. See you around.