

If you want cheap encrypted storage you can run a Nephele server with encryption and something like Backblaze B2.
I’m Hunter Perrin. I’m a software engineer.
I wrote an email service: https://port87.com
I write free software: https://github.com/sciactive


If you want cheap encrypted storage you can run a Nephele server with encryption and something like Backblaze B2.


Yes, that’s why degloogled Android is best. It doesn’t matter if you use privacy centric apps if your OS is spying on you.


I see a lot of people in here shitting on iOS and not Google. Stock Android is worse than iOS for privacy. Unless you’re going to run a degoogled Android, don’t bother getting rid of iOS. But degoogled Android is the best option, if you can.


deleted by creator
I love that this is an article… a text article.


The way I’ve done it is Ubuntu Server with a bunch of Docker Compose stacks for each service I run. Then they all get their own subdomain which all runs through the Nginx Proxy Manager service to forward to the right port. The Portainer service lets me inspect things and poke around, but I don’t manage anything through it. I want it all to be super portable, so if Ubuntu Server becomes too annoying, I can pack it all up and plop it into something like Fedora Server.


They can’t do 4K video. The best they can do is 1080p30.


I didn’t say Raspberry Pi Zero. Those are niche machines. They’re not fast enough to do general purpose computing.


2.4 times. But, who’s counting?


No. They emulate a keyboard, and use the keyboard shortcuts to do things in Windows. So they won’t work out of the box in Linux, but you can add each of the keys as a keyboard shortcut, then they’ll work.


I’d recommend the Pepper Jobs windows 10 gyro remote. I’ve got two of them because they’re so great.


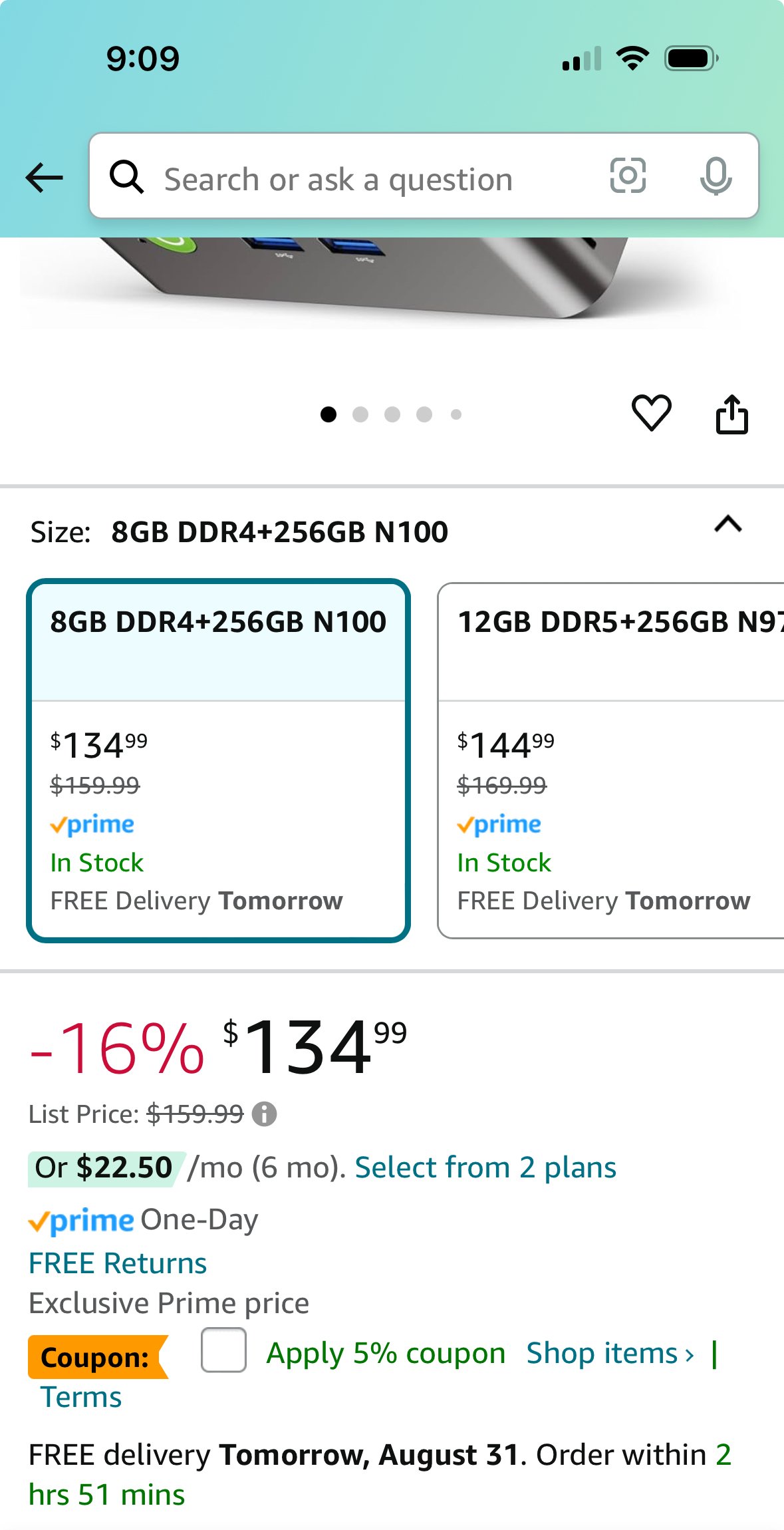
Exactly. N100 mini PCs are like the Swiss Army Knife of computers. Almost as compact as a Raspberry Pi, and compatible with a lot more things.


Because either money or cult like following.


Shadowsocks doesn’t look anything like HTTPS traffic. It looks like a bare stream cipher over TCP connections to one host with bursts of traffic. HTTPS starts off with a TLS handshake (a client hello, a server hello, the server certificate, then a cipher negotiation and key exchange) before any ciphertext is exchanged. Shadowsocks just starts blasting a ciphertext stream. Even if you run it on port 443, it looks nothing like HTTPS.
Without any sort of cipher negotiation and key exchange, it’s obvious that it’s a stream cipher with a pre shared key, so this would be automatically suspicious. There’s also not really any plausible deniability here. If they probe your Shadowsocks host and see it running there, that’s all the proof they need that you’re breaking their rules. With a VPN, you could at least say it’s for a project, and with SSH, you could say you’re just transferring files to your own machine.


I mean, they could have used their eyeballs, but we don’t know, because he didn’t say.
Shadowsocks would work, but I feel like bare stream ciphers over TCP are a dead giveaway that you’re bypassing content restrictions. Especially if they probe that host and see it running. But, what do I know? It’s just my job five days a week.


It very much is. I used it regularly in both high school and college. In high school it was just how I connected to other machines. One of my teachers taught me how to use it. In college we were told to use it by the professor, so at least one entire class was using it for every assignment. That’s pretty normal in any school that has programming or networking courses.
SSH is usually used for work, so it just looks like someone working. Tor is used for nefarious purposes, so it will always look suspicious. VPNs are used to bypass content restrictions, so they will always look suspicious.


They said they got in trouble for Tor, they didn’t say their machine was identified. Even if it was, yet again, there’s nothing suspicious about SSH traffic. SSH traffic looks like work (because it usually is).
And I’ll ask you again, since you avoided the question, what better way is there? What would look more innocent than SSH?


I helped out with my high school network and SSH absolutely would not have looked suspicious. I can’t say for this school, but that was a regular part of the curriculum in mine. Even if it wasn’t, what are you gonna do as a net admin? You have zero evidence that a student is doing something malicious.
I feel like you’re a script kiddy who got called out for being overly confident online, and now you’re grasping at straws. I literally gave you two outs, and you doubled down every time. There is nothing suspicious about SSH traffic, even in a high school network, let alone a college network, and if you think there is, you’re 100% brand new to the industry.
You still haven’t given any alternative that would look any less suspicious than SSH traffic, and you still haven’t given any method a net admin could use to identify your machine from the countless others that connect to an open WiFi network.
In fact, let’s test you. There’s something that old versions of Firefox will expose, even through a SOCKS proxy. What is it, and what did Firefox introduce to prevent that?


These aren’t assumptions. OP states it’s an open WiFi network in their post, and unless you name your computer after yourself, all the network admins can see is your MAC address. And what is suspicious about SSH traffic? And what better way is there? VPN traffic will look more suspicious.
What do you do for a living? I’m a software and network engineer, so this is in my realm of expertise. All the network admins will see is OP’s MAC and that they’re sending a lot of SSH traffic to a Digital Ocean IP (if they even bother to sniff their traffic). This is how I, as a network engineer, have personally bypassed content filters.
Reolink has a local encrypted video doorbell.