

Native? Isnt it a web app?
Global namespace extremist. Defragment your communities!


Native? Isnt it a web app?
Gmail offers imap amd smtp access. You have to enable 2FA, and then it will allow you to create account for so called “less secure apps”.
In your place, I’d either continue using gmail directly, or finish the configuration of the self hosted mail server and just use that with any smtp/imap client. I suggest getting a separate domain for testing first, before moving your primary inbox there.


you still need good security configuration of the exposed service.
In a sense that security comes in layers, yes. But in practice, this setup will prevent 100% of bots scanning the internet for exposed services, and absolute majority of possible targeted attacks as well. It’s like using any other 3rd party VPN, except there’s not a central point for the traffic to flow through.
From the attackers point of view, nothing is listening there.
I’ve used a similar setup in the past to access a device behind a NAT (possibly multiple NATs) and a dynamic IPv4. Looking back, that ISP was a pure nightmare.


This is not a guide to hide from the government or ISP. Just a way to tunnel to your home server without publishing the sshd for random strangers. Personally, I’d just publish the ssh and be done with it.
I would rather live without the correlation attacks
The more people using Tor, the less useful targeted disconnects become.


Which is still just as open, but also a massive calling card for anyone trolling around the TOR network
Luckily, it is no longer possible to easily sniff the new v3 addresses by deploying a malicious relay. Any attack to even reveal the existence of a hidden service would require a very specialized setup. And we’re just talking discovery, not the ability to connect and attack the actual service running there.


just connecting to Tor is very much a huge exposure imho
Exposure of what, to whom?


"GhostWrite is the result of an architectural flaw, a hardware bug in the XuanTie C910 and C920 CPU. These are only two of many RISC-V CPUs, but they are widely used for a variety of applications. According to the research team, vulnerable devices include:
Scaleway Elastic Metal RV1, bare-metal C910 cloud instances


Of course security comes with layers, and if you’re not comfortable hosting services publically, use a VPN.
However, 3 simple rules go a long way:
Treat any machine or service on a local network as if they were publically accesible. That will prevent you from accidentally leaving the auth off, or leaving the weak/default passwords in place.
Install services in a way that they are easy to patch. For example, prefer phpmyadmin from debian repo instead of just copy pasting the latest official release in the www folder. If you absolutely need the latest release, try a container maintained by a reasonable adult. (No offense to the handful of kids I’ve known providing a solid code, knowledge and bugreports for the general public!)
Use unattended-upgrades, or an alternative auto update mechanism on rhel based distros, if you don’t want to become a fulltime sysadmin. The increased security is absolutely worth the very occasional breakage.
You and your hardware are your worst enemies. There are tons of giudes on what a proper backup should look like, but don’t let that discourage you. Some backup is always better than NO backup. Even if it’s just a copy of critical files on an external usb drive. You can always go crazy later, and use snapshotting abilities of your filesystem (btrfs, zfs), build a separate backupserver, move it to a different physical location… sky really is the limit here.


Distraction free? Look at all those number buttons looking like little faces. They WILL judge you, as you type. I’m pretty sure about that.


Why would you punish my innocent budget with filthy ideas like this?
You know the marketing brainwashing works, when people go look for exclusive games :D


What’s wrong with the lightbulbs? I have pretty good experience with all their zigbee products. Cheap, reliable, stable, sturdy, works with Home Assistant.


It says right there
This is the point where I start to worry about my reading comprehension. It’s too late for a severe case of ADHD, and too early for a dementia. What the fuck, brain!?


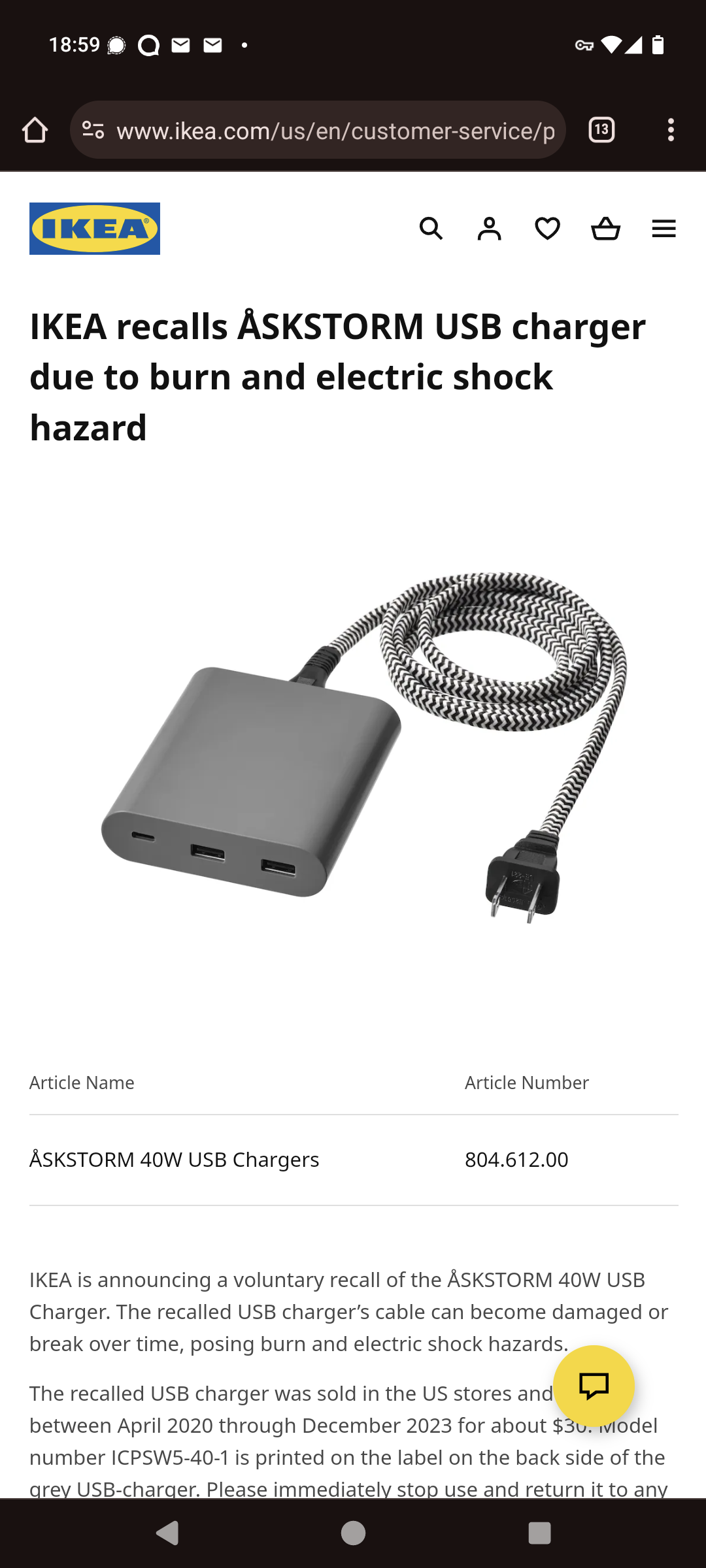
First thing I found on the ikea website is a recall of the older USB charger.


I’ve recently got my hands on a laptop with 3 different versions of Teams. And broken updates…


There are instances that work without an account still. It’s the main benefit of the whole thing.


Isn’t that mainly a problem with recursive DNS servers? The authoritative servers are only aware of the few domains they’re hosting.
That’s because they’re not going to actually do it.